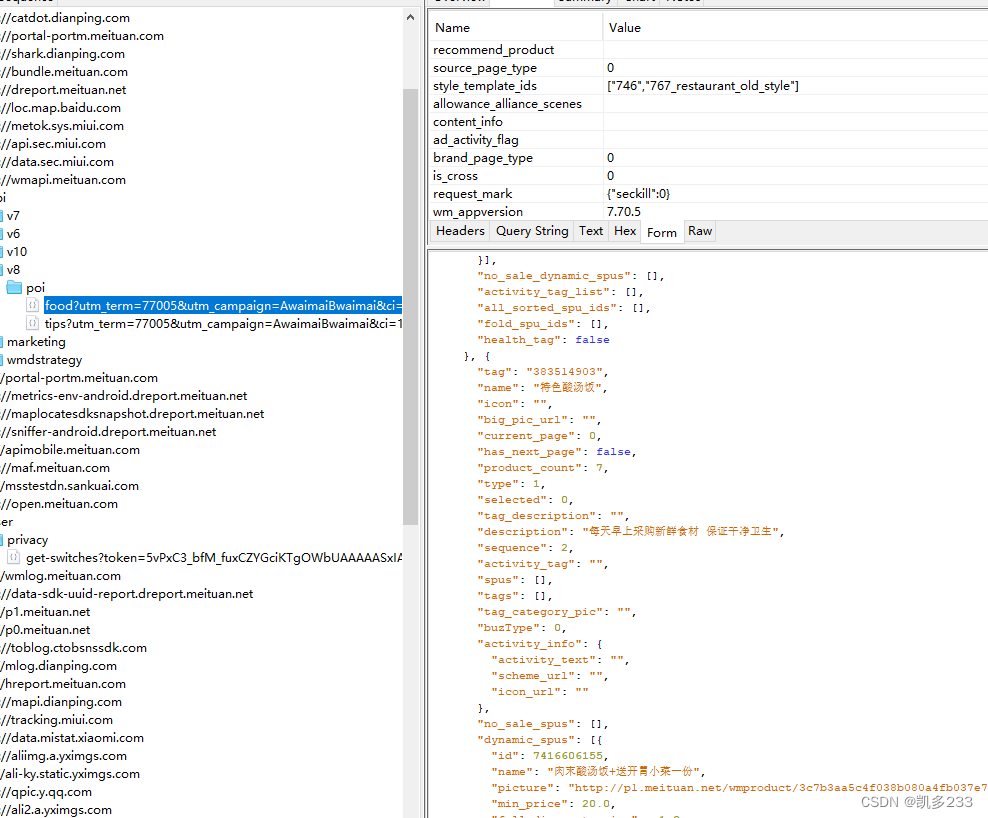
一、抓包分析
通过Charles进行抓包
模拟构造请求:
headers = {
“mtgsig”: “{}”, //mtgsig加密,这里面一堆参数
“retrofit_exec_time”: “1655260135126”, //时间戳
“M-SHARK-TRACEID”: “”,
“User-Agent”: “”,
“Host”: “wmapi.meituan.com”
}
url = “https://wmapi.meituan.com/api/v8/poi/food”
params = {
“utm_term”: “77005”,
“utm_campaign”: “AwaimaiBwaimai”,
“ci”: “107”,
“utm_medium”: “android”,
“uuid”: “”, //自己设备uuid
“utm_source”: “”,
“utm_content”: “3e5cfefe55dac40c”, //固定值,这个加密时会用到
“region_id”: “”,
“region_version”: “1655260112773” //时间戳
}
data = {
“group_chat_share”: “”,
“wm_poi_id”: “925193045727712”, //这个是店铺id,更换这个就能获取不同店铺商品数据
“recall_type”: “0”,
“search_word”: “”,
“search_log_id”: “”,
“page_index”: “0”,
“recommend_product”: “”,
“source_page_type”: “0”,
“style_template_ids”: “”,
“allowance_alliance_scenes”: “”,
“content_info”: “”,
“ad_activity_flag”: “”,
“brand_page_type”: “0”,
“is_cross”: “0”,
“request_mark”: “{\”seckill\”:0}”,
“wm_appversion”: “7.70.5”, //版本号
“wm_ctype”: “android”,
“userid”: “”,
“uuid”: “”,
“platform”: “4”,
“personalized”: “1”,
“wm_latitude”: “26616827”,
“wm_actual_longitude”: “106643562”,
“content_personalized_switch”: “0”,
“ad_personalized_switch”: “0”,
“wm_visitid”: “”,
“wm_dversion”: “”,
“wm_mac”: “”,
“wm_logintoken”: “”,
“push_token”: “”,
“app”: “4”,
“oa_id”: “”,
“wm_longitude”: “106641205”,
“wm_actual_latitude”: “26618857”,
“wm_did”: “”,
“version”: “7.70.5”,
“app_model”: “0”,
“wm_dtype”: “”,
“wm_uuid”: “”,
“partner”: “4”,
“seq_id”: “58”,
“wm_channel”: “1061”,
“request_id”: “”,
“waimai_sign”: “”, //waimai_sign加密
“wm_seq”: “33”,
“req_time”: “1655260135696” //时间戳
}
response = requests.post(url, headers=headers, params=params, data=data)
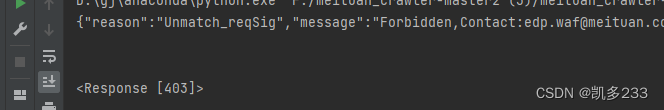
账号和设备风控不谈,经过尝试,想要请求不同店铺数据,只有正确构造出“mtgsig”、”waimai_sign”两个参数才行,不然就会返回403
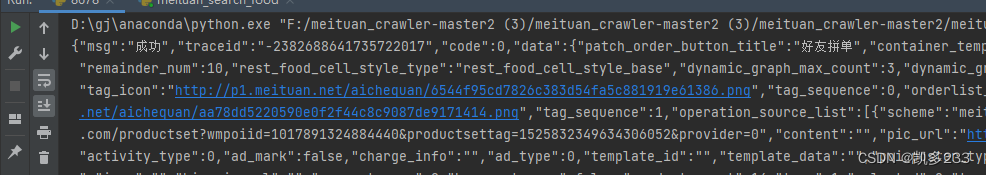
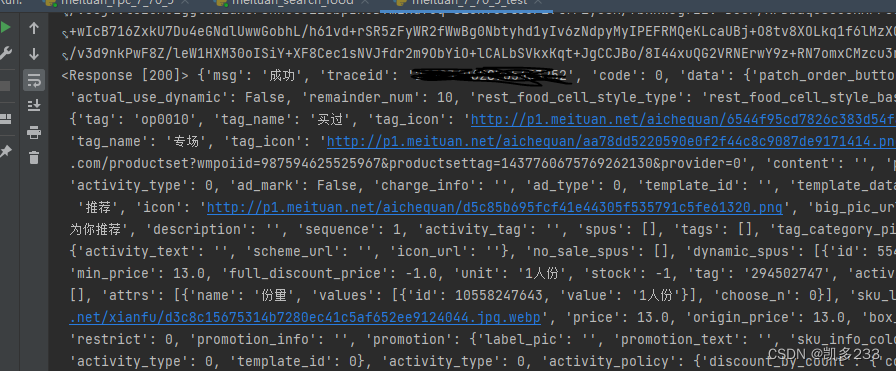
正常返回:
“mtgsig”、”waimai_sign”任何一个参数不对返回:
二、参数分析
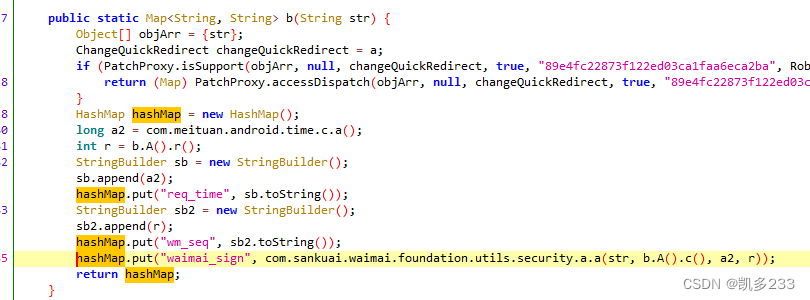
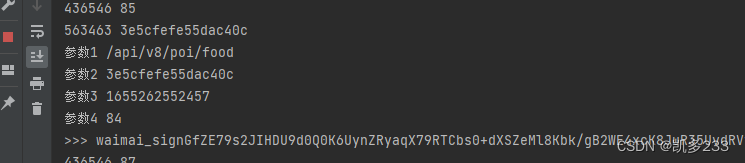
1、通过jadx-gui分析apk ,首先全局搜索waimai_sign,这个很简单一下就搜出来了
hook下这个函数
有四个参数,参数1是url后半部分,参数4是时间戳,
参数2和4是:
var bb = Java.use(“com.sankuai.waimai.platform.b”);
console.log(bb.A().r()) 对应”wm_seq”
console.log(bb.A().c()) 对应”utm_content”
参数都知道了就能构造参数进行rpc调用了,具体代码就不写了。
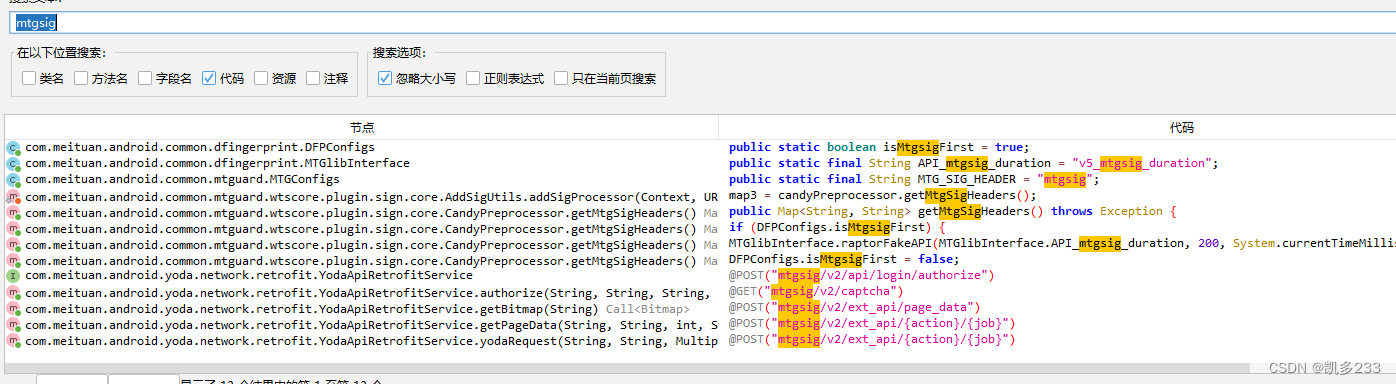
2、再来全局搜索mtgsig
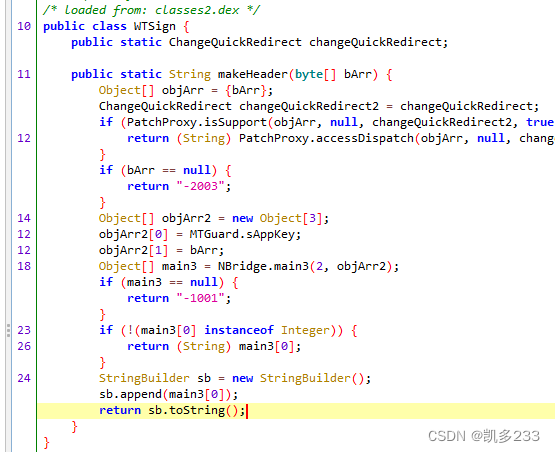
进入getMtgSigHeaders,一层一层点进去,最后会看到
hook下该函数:
参数是由”POST /api/v8/poi/food “加上params和data里面的参数拼接出来的,注意要排序,所以一定要先算出waimai_sign,waimai_sign的值也会拼接在请求mtgsig参数里面
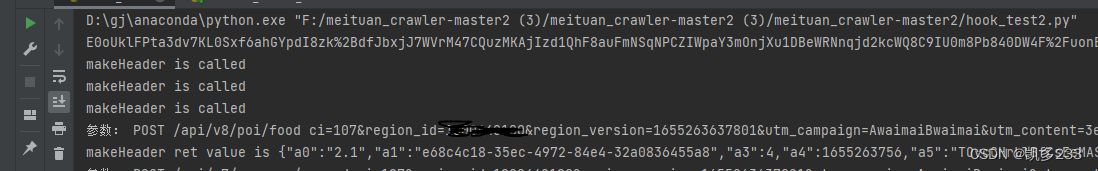
三、测试
最后构造参数,进行rpc调用,成功模拟出两个参数值,测试出来结果也是可用的,成功跑出数据(○゚ε゚○)
————————————————
版权声明:本文为CSDN博主「凯多233」的原创文章,遵循CC 4.0 BY-SA版权协议,转载请附上原文出处链接及本声明。
原文链接:https://blog.csdn.net/qq_44628911/article/details/125303004
您可能感兴趣:
微信扫描下方的二维码阅读本文